Recently, I had the honor of talking to David Bombal about the TLS Handshake. We picked apart everything that occurs in the first few milliseconds every time you browse to an HTTPS website:
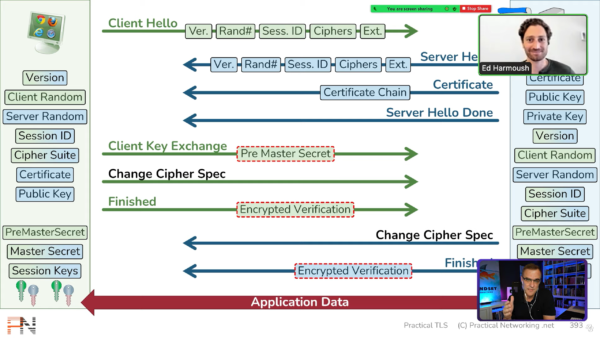
In the video we stepped through every message of the Handshake, and spoke in detail about what information is included in each message and how that information is used.
The ultimate goal of the TLS handshake is to derive Session Keys, these are the keys which actually Encrypt and Secure the data transfer between the Client and the Server. And in this TLS deep dive, we explained exactly how those Session Keys are derived.
In the video, we also stepped through a Packet Capture showing a TLS Handshake using the RSA Key Exchange. You can download the Packet Capture and inspect it yourself using Wireshark.
Practical TLS
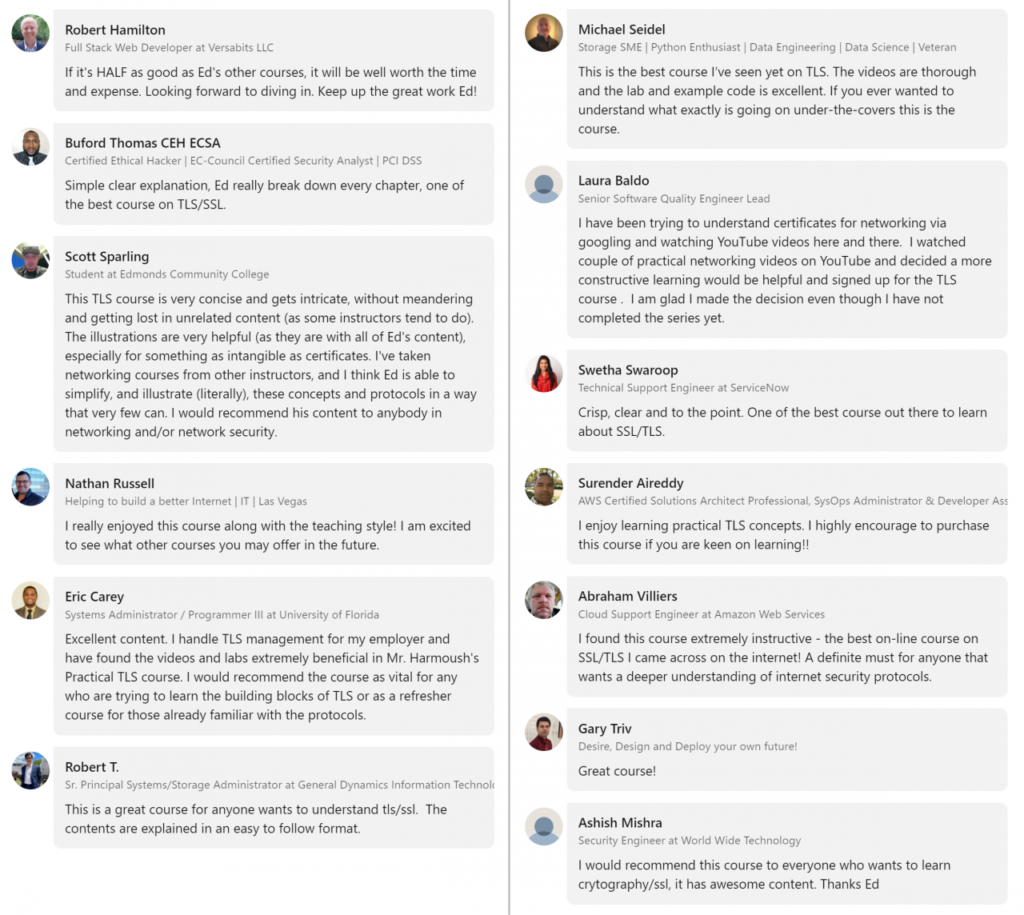
The slides and content we walked through in the video is from my TLS Deep Dive course: Practical TLS.
It’s a meticulously crafted, thorough examination of the entire SSL and TLS ecosystem. In the course we walk through everything needed to take anyone from Security and Crypto amateur to an SSL Expert.
But don’t take my word for it, see what others have said about the course:
You can also check out the first two modules (and a few other lesson) for free to make your own decision about the quality of the course:
Great Timing Twitter…
In unrelated news, the day this video released is also the day Twitter decided to do a profile review. 🤦♂️🤦♂️

Thanks Twitter… great timing.
If you are trying to connect with me on Twitter and see something like this, either click through “Yes, view profile”, or give it a few days. But, please do connect with me on my new Twitter account =)

That was a great presentation.
Thanks Azza!
Loved the video, even though I am a newbie to the world of IT and I didn’t quite get all of it by the end I was quite excited by how it all works. Very interesting and well explained, ill be watching that again. Thankyou.
Glad you enjoyed it!
I was looking for your discount code. Where can I find it?
In the first comment of this video: https://www.youtube.com/watch?v=P1v6QA0W7Xw
Best SSL/TLS explanation video I’ve seen. Is it possible to share private key for blue.com for lab purposes?
I provide the key in the course as a lab. It’s Lab 6.4 in the curriculum where we decrypt the TLS conversation. Hope you can join the course =)
how much money can I make for knowing this, ‘.
/\
?
Thank you very much for such a great explanation on handshake
The Packet Capture is no longer available 🙁
Hi, thanks for the perfect video. COuld you please upload the Wireshark PCAP file again? it is not available anymore.
Thanks alot!
hello ,
where have you private keys ? and why i need to have ssl_keys.log file to decrypt https et private key to decrypt tls ? is it not the same encryption ?
Cordially
Re: the PCAP: “8026 This link has been deleted by the owner.”
Hello Ed
You course is just GREAT it is the best source availabl for TLS.
I am asking if you offer the slides ( power poinr, pdf) for your TLS course ( free part on youtube) so I can use it while teaching to my students
Hi Ed,
Im a student
I cannot afford 297USD cost.
I would appreciate it if you could send me a discount
Yossi