This article is a part of a series on Packet Traveling — everything that happens in order to get a packet from here to there. Use the navigation boxes to view the rest of the articles.
The Open Systems Interconnect model (OSI Model) explains all the individual functions that are necessary for the Internet to work.
It is a set of seven independent functions which combine to accomplish the end-goal of Computer to Computer communication.
Much like a car is composed of independent functions which combine to accomplish the end-goal of moving the car forward: A battery powers the electronics, an alternator recharges the battery, an engine rotates a driveshaft, an axle transfers the driveshaft’s rotation to the wheels, and so on and so forth.
Each individual part can be independently replaced or worked on, and as long as each individual part is functioning properly, the car moves forward.
The OSI model is divided into seven different layers, each of which fulfills a very specific function. When combined together, each function contributes to enables full computer to computer data communication.
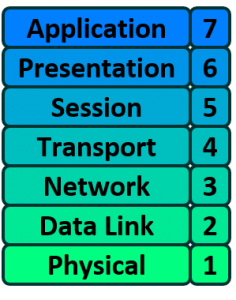
In the rest of this article, we will look at each of the individual layers of the OSI model and their individual responsibility.
OSI Layer 1 – Physical
The Physical layer of the OSI model is responsible for the transfer of bits — the 1’s and 0’s which make up all computer code.
This layer represents the physical medium which is carrying the traffic between two nodes. An example would be your Ethernet cable or Serial Cable. But don’t get too caught up on the word “Physical” — this layer was named in the 1970s, long before wireless communication in networking was a concept. As such, WiFi, despite it not having a physical, tangible presence, is also considered a Layer 1 protocol.
Simply put, Layer 1 is anything that carries 1’s and 0’s between two nodes.
The actual format of the data on the “wire” can vary with each medium. In the case of Ethernet, bits are transferred in the form of electric pulses. In the case of Wifi, bits are transferred in the form of radio waves. In the case of Fiber, bits are transferred in the form of pulses of light.

Aside from the physical cable, Repeaters and Hubs also operate at this layer.
A Repeater simply repeats a signal from one medium to the other, allowing a series of cables to be daisy chained together and increase the range a signal can travel beyond the single cable limit. These are commonly used in large WiFi deployments, where a single WiFi network is “repeated” throughout multiple access-points to cover a larger range.
A Hub is simply a multi-port Repeater. If four devices are connected to a single Hub, anything sent by one device gets repeated to the other three.
OSI Layer 2 – Data Link
The Data Link layer of the OSI model is responsible for interfacing with the Physical layer. Effectively, Layer 2 is responsible for putting 1’s and 0’s on the wire, and pulling 1’s and 0’s from the wire.
The Network Interface Card (NIC) that you plug your Ethernet wire into handles the Layer 2 functionality. It receives signals from the wire, and transmits signals on to the wire.
Your WiFi NIC works the same way, receiving and transmitting radio waves which are then interpreted as a series of 1’s and 0’s.
Layer 2 will then group together those 1’s and 0’s into chunks known as Frames.
There is an addressing system that exists at Layer 2 known as the Media Access Control address, or MAC address. The MAC address uniquely identifies each individual NIC. Each NIC is pre-configured with a MAC address by the manufacturer; in fact, it is sometimes referred to as the Burned In Address (BIA).

Aside from your NIC, a Switch also operates at this layer. A Switch’s primary responsibility is to facilitate communication within Networks (this idea will be expanded upon in a later article in this series).
The overarching function of the Data Link layer is to deliver packets from one NIC to another. Or to put it another way, the role of Layer 2 is to deliver packets from hop to hop.
OSI Layer 3 – Network
The Network layer of the OSI model is responsible for packet delivery from end to end.
It does this by using another addressing scheme that can logically identify every node connected to the Internet. This addressing scheme is known as the Internet Protocol address, or the IP Address.
It is considered logical because an IP address is not a permanent identification of a computer. Unlike the MAC address which is considered a physical address, the IP address is not burned into any computer hardware by the manufacturer.
 Routers are Network Devices that operate at Layer 3 of the OSI model. A Router’s primary responsibility is to facilitate communication between Networks. As such, a Router creates a boundary between two networks. In order to communicate with any device not directly in your network, a router must be used.
Routers are Network Devices that operate at Layer 3 of the OSI model. A Router’s primary responsibility is to facilitate communication between Networks. As such, a Router creates a boundary between two networks. In order to communicate with any device not directly in your network, a router must be used.
OSI Model – Layer 2 vs. Layer 3
The interaction and distinction between Layer 2 and Layer 3 is crucial to understanding how data flows between two computers. For example, if we already have a unique L2 addressing scheme on every NIC (like MAC addresses), why do we need yet another addressing scheme at L3 (like IP addresses)? Or vice versa?
The answer is that both addressing schemes accomplish different functions:
- Layer 2 uses MAC addresses and is responsible for packet delivery from hop to hop.
- Layer 3 uses IP addresses and is responsible for packet delivery from end to end.
When a computer has data to send, it encapsulates it in a IP header which will include information like the Source and Destination IP addresses of the two “ends” of the communication.
The IP Header and Data are then further encapsulated in a MAC address header, which will include information like the Source and Destination MAC address of the current “hop” in the path towards the final destination.
Here is an illustration to drive this point home:
Notice between each Router, the MAC address header is stripped and regenerated to get it to the next hop. The IP header generated by the first computer is only stripped off by the final computer, hence the IP header handled the “end to end” delivery, and each of the four different MAC headers involved in this animation handled the “hop to hop” delivery.
OSI Layer 4 – Transport
The Transport layer of the OSI model is responsible for distinguishing network streams.
At any given time on a user’s computer there might be an Internet browser open, while music is being streamed, while a messenger or chat app is running. Each of these applications are sending and receiving data from the Internet, and all that data is arriving in the form of 1’s and 0’s on to that computer’s NIC.
Something has to exist in order to distinguish which 1’s and 0’s belong to the messenger or the browser or the streaming music. That “something” is Layer 4:
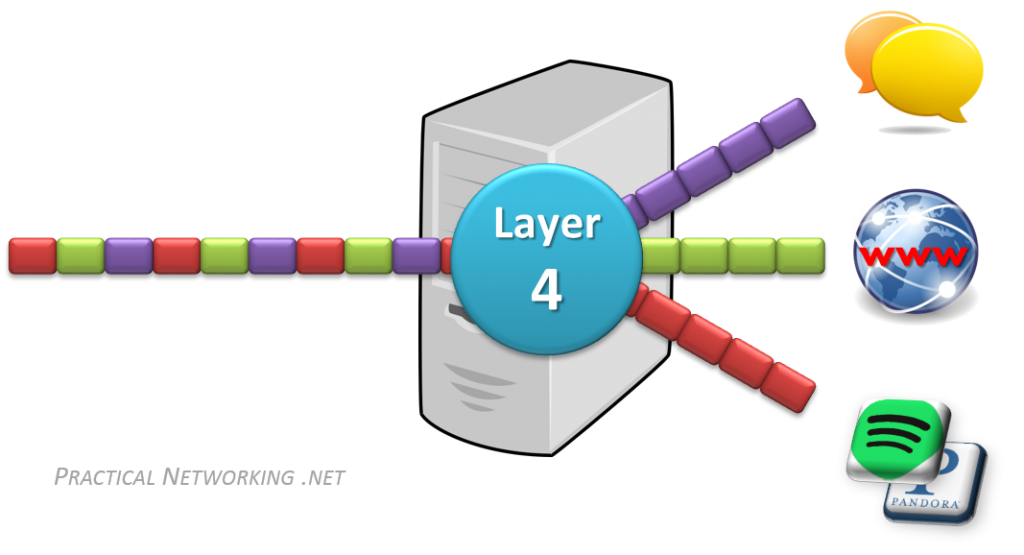
Layer 4 accomplishes this by using an addressing scheme known as Port Numbers.
Specifically, two methods of distinguishing network streams exist. They are known as the Transmission Control Protocol (TCP), or the User Datagram Protocol (UDP).
Both TCP and UDP have 65,536 port numbers (each), and a unique application stream is identified by both a Source and Destination port (in combination with their Source and Destination IP address).
TCP and UDP employ different strategies in how data streams are transferred, and their distinction and inner workings are both fascinating and significant, but unfortunately they are outside the scope of this article series. They will be the topic of a future article or series.
To summarize, if Layer 2 is responsible for hop to hop delivery, and Layer 3 is responsible for end to end delivery, it can be said that Layer 4 is responsible for service to service delivery.
OSI Layer 5, 6, and 7
The Session, Presentation, and Application layers of the OSI model handle the final steps before the data transferred through the network (facilitated by layers 1-4) is displayed to the end user.
From a purely Network Engineering perspective, the distinction between Layers 5, 6, and 7 is not particularly significant. In fact, there is another popular Internet communication model known as the TCP/IP model, which groups these three layers into one single encompassing layer.
The distinction would become more significant if you were involved in Software Engineering. But as this is not the focus of this article series, we will not dive deep into the differences between these layers.
Many network engineers simply refer to these layers as L5-7 or L5+ or L7. For the remainder of this series, we will do the same.
Encapsulation and Decapsulation
The last item we need to discuss before we move on from the OSI Model is that of Encapsulation and Decapsulation. These terms refer to how data is moved through the layers from top to bottom when sending and from bottom to top when receiving.
As the data is handed from layer to layer, each layer adds the information it requires to accomplish its goal before the complete datagram is converted to 1s and 0s and sent across the wire. For example:
- Layer 4 will add a TCP header which would include a Source and Destination port
- Layer 3 will add an IP header which would include a Source and Destination IP address
- Layer 2 would add an Ethernet header which would include a Source and Destination MAC address
On the receiving end, each layer strips the header from the data and passes it back up the stack towards the Application layers. Here is the whole process in action:
Note that this is only an example. The header that will be added will be dependent on the underlying communication protocol. For instance, a UDP header might be added at Layer 4 instead, or an IPv6 header might be added at Layer 3.
Either way, it is important to understand that as data is sent across the wire, it gets passed down the stack and each layer adds its own header to help it accomplish its goal. On the receiving end, the headers get stripped off one at a time, layer by layer, as the data is sent back up to the Application layer.



Damn dude this is sickkkk
AGree
Glad you two enjoyed it!
Ik zie dat je een dubbele authenticatie aan het staan maar het werkt niet
You get a lot of respect from me for writing these helpful areitlcs.
Glad you enjoy them, Belle. More are always on the way.
THIS IS A GREAT TUTORIAL. I HAVE BEEN READING ABOUT THIS STUFF ALL WEEK AND NOW IT REALLY MAKES SENSE. THANK YOU SO MUCH
Brilliant site ! The moving diagrams / animations really brings these topics to life and gives massive understanding of usually complex concepts.
Thanks a lot for the efforts.
Thank you for the kind words =) I’m happy you found these articles helpful ^_^.
Actually very good article and made me clear in lots of concepts about osi model
Glad you liked it, Nabeel. Thank you for the comment. =)
John Johnathan, you are a kanker mongool
I coudn’t agree more
Thanks alot for seeing this good site!
You’re welcome, Aye. Glad you enjoyed it.
Hi Ed,
“The overarching function of the Data Link layer is to deliver packets from one NIC to another. Or to put it another way, the role of Layer 2 is to deliver packets from hop to hop.”
Doubt: Data link layer delivers the Frame to Network layer where it gets de-encapsulated and we get packet there, am I correct? As in above statement of yours you mentioned layer 2 delivers the packets. Also, how NIC can deliver the packets as its PDU is bits.
Thanks,
Vishwa
Hi Vishwa,
The combination of [IP][PAYLOAD] is known as a packet. And the combination of [ETH][PAYLOAD] is known as a frame.
In the above, the [ETH] header is the L2 header, and inside the frame’s payload is the packet ([IP][PAYLOAD]). So yes, L2 will deliver the packet to the next NIC.
That said, keep in mind the terms Frame and Packet are often used interchangeably in the industry.
Hope this helps.
Thank you for an explanation Ed, that’s helpful.
Vishwa 🙂
Excellent post. I was checking conintuously this weblog and I’m impressed! Extremely useful info specifically the final part I care for such info a lot. I was seeking this particular information for a very lengthy time. Thanks and good luck.
Ok I get it. Data link layer will receive the packet from network layer that contains the IP header. Then it will add the ETH header in it and form a frame. Then what?
I am really confused about these two. After frame we have two more steps that are bits and signals(signal depending on the medium of transfer like radio waves for wifi and electric signals for ethernet). So what actually happens. And also all the above units like frame, packet, segment, what are they actually? Aren’t they also bits since computers process data in terms of bits
Hi Nikhil, yes they are all made up of bits. You should take a look at Ethernet and IP headers (e.g. on Wikipedia) to see how they are constructed. Another way to look at this data is with WireShark, which is a free packet inspection application, or with Cisco’s Packet Tracer in simulation mode (also free, you have to sign up with Cisco to get access).
Hi Steven. Thanks for the response. Will try those tools. But I was asking that ethernet frame needs to be converted into bits, and then finally to signals. So after data link layer forms the frame, what happens exactly.
Hi Nikhil. Great questions. Be careful not trying to explicitly fit everything into one layer… the OSI model is just a model, it’s just a teaching tool. The TCP/IP stack is the model actually implemented on operating systems, and TCP/IP combines OSI L1 and L2 into a single layer. Meaning the “function of adding a L2 header and turning the packet into Frames” and “transmitting bits across the wire” is handled by the same process.
On way or another, both items are done (header + converted to bits). The distinction of exactly when either happens is ambiguous, and likely not overly helpful when trying to understand Networking.
Hope this helps.
Thanks Ed. That makes sense now
HI..Nice document
Hi Rajendra, glad you liked it!
This has to be the most extraordinary explanation work I ever came across since browsing the Internet.
That someone has the talent to make things that clear and the desire to put such a content available to all of us is unbelievable.
Hi Almudena, glad you enjoyed it, and thank you for such kind words! This article has indeed become one of my favorites to share with others, so much so that I set up an easy shortcut: pracnet.net/osi.
Such an amazing discovery this site is for me. Thanks so much for sharing this with us!
Nice article dude. Thanks! Do you have an article for layers 5 6 7 as well?
Hi Ashwin, I’m afraid I don’t cover L5-7 more thoroughly than I do in this article. I did answer a question on Reddit that involved explaining L5, L6, and L7 that might help make sense of it in your mind.
This is the best of its kind.
easy to understand!!!!
very Helpful!!!!!!!!!!!
Your animation drives the concept deeper and remains sealed in my mind. I can just close my eyes and visualize. Thanks for the great visualization…outstanding.
The best explanation of the OSI model I have seen so far. My computer networks professor can’t be even remotely compared. Hands down!
Really well worded article! This is a very good series and was a fun read! My boss looked at me weird when he saw me reading about the OSI model when I have my CCNA but I believe that refreshing on the basics will ALWAYS be important and will allow you to even further strengthen your foundation, even if you are already standing tall.
But back to putting credit to where it is due. I have to agree with several responses here, this is by far one of the best representations of the OSI models I have ever seen. The vocabulary and way it is explained is easy to get without rereading (unlike the Cisco books) and the diagrams are very helpful (… Again unlike the Cisco books and other sources).
I will look forward to seeing additional prints if you decide to make more. I thought I saw a comment somewhere asking to go more in depth with the 5-7 layers. And yes it is true it’s not really a need-to-know thing in the IT world, but it would be a great thing to learn, and I feel that if you explained it, it would help A LOT of people to understand it in stead of those layers being this vague, magical, thing . . . that does stuff. Because that’s what plenty of people think, especially novices or beginners in the networking field.
Once again, an amazing article, very thorough, nicely worded, and obviously very passionately wrote.
The best text lecture on topic.
Wonderful (clappings)… thanks
hi,
Thank you for explaining in a simple way.
i have a question– i heard that there are 3 types of sessions .resumable,non-resumable and null session can you please explain about this?
In Session layer
Hi Krishna, glad you enjoyed the articles.
The rules for the Session, Presentation, and Application layer are much less clearly defined. Essentially, these layers answer these questions:
Session – How do we keep one user’s session separate from another? How do we keep multiple transactions from the same user independent from one another?
Presentation – In what format is the data transferred? Letters? If so, ASCII or EBCDIC? Binary? If so, big endian or little endian? etc
Application – What sequence(s) of data make up actual data structures or transactions? For example, in FTP the sequence of letters “LIST” issue a command to view the files on a remote FTP server. In HTTP, the sequence of letters “GET” issue a command to retrieve an webpage.
Remember, once we get to these three it varies greatly between different applications. To that end, I am unable to speak specifically to what you have read as “resumable, non-resumable, and null sessions”. It could mean many different may things for many different applications.
Hope this helps.
HI,
Bro, your video on Youtube was awesome. I even can’t think that it was too easy in that way to understand Layer 2 Layer 3 Arp and function of switch, router and packet flow.
I think you should make more video on computer networking, it will be great help to everyone.
mainly on the topic such as DNS DHCP VLAN and all
Regards
Jony
Hi Jony,
Glad you enjoyed them! Making more videos is on my list. As is publishing more articles.
You mentioned VLANs, have you seen the VLAN articles? You can see all of them with this short link: pracnet.net/vlans. I hope you enjoy them as much as the other video / articles!
Just made that so much clearer than my Cisco courses ever did.
Thank you!!!
How does the layer 2 knows the target MAC address ?
I know as soon as I sent the message, I know the source IP, MAC and also destination IP, but how can I know the destination MAC , as it is specify here:
Layer 2 would add an Ethernet header which would include a Source and Destination MAC address
Hi Ysidro, great question!
The destination MAC address is resolved using the Address Resolution Protocol, or ARP.
Great explanation. Would like if you could cover more topics. Looking forward to your further posts.
This is VERY helpful. Thank you!
Amazing article, thanks for posting this, very useful ! Very well explained too.
Hello Ed,
Your articles are really great. It’s so simple and easy to.understand and visualise that we don’t have to browse to another sites to clear our networking concepts.
You are really boon for network engineer like us.
Keep continuing such beautiful teaching and looking for more articles.
You are truly the best tutor. God bless you.
very nice article and clear explaination
Neat stuff, it really helped me in understanding the concept in a better way. Thank you!
Wow! Informative, Thanks Man.
to understand osi this is the end…..
Crystal Clear. Makes the foundation strong.
Awesome. Thanks a lot for the good work.
Hello there ! hope so you doing great mayn same I am feeling right now after reading your article .well Please tell me one thing ? does mac address changes on every node like when our packet send to router with src and destination mac addr then how new src and destination mac address makes up I am confused as far as I know router only have one macAddress with one NIC card
Loved the explanation!! Thank you so much !!!
Super Awesome Explanation…
Thanks a lot for wonderful articles.
All of your articles are a great source of information with clarity, granularity & preciseness.
Incredible!
SUPER COMPREHENSIVE. UNDERSTOOD what i was able to uderstand in the last two years.
Thanks you xoooooooooooooo much sir 🙂
I see the whole world of network in a couple of minutes. thank to u and god I meet this. no more boring!!!
Hi Ed… How can I get full material to study???
these are great. thanks for these articles
I just have one word on the blog, AWESOME!!
OMG, the best ever article, thanks a lot!
8 years excluding college – this is the first time I understood OSI Model . Thank you so much.
Tremendous article!! Many thanks 😀
Networking has become a pleasure to study
Love the animations. They help me understand the concept very effectively.
This is TECHNICAL SEX!
Thanks a ton, I never read something like this in such a simple language.
This is an awesome break down of the OSI model! Thank you.
This is AWESOMEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEEE
Amazing Explanation , i will be so grateful if you could clear my 1 confusion ,
i have read that session layer’s responsibility is to start , maintain and terminate the session but we always learn that its the job of tcp to establish a connection via 3-way handshake , whats the difference between the sessions at Session and Transport Layer?
Each layer, in a way, maintains it’s own “session”. For example, L3 maintains a session between two IP addresses. L4 maintains a session between two ports (this is where TCP lives). L5+ might maintain sessions between two different users. Think of HTTP cookies, for example, they are arriving on TCP port 80, but it’s possible an application wants to differentiate multiple user streams within each “TCP port 80” stream. Hence, you need another “session” distinguisher.
Thanks a lot Ed , your explanations are always very amazing. #Respect
Dear Eddie..
Thanks for uploading this content for all of us n really appreciate for your way of explanation. I have seen your youtube videos too. It was simply amazing!! Kindly upload more videos.
May God bless you!!
Shine
You’re welcome! Glad you enjoyed the content!
its 2019 and i still regard this as the clearest explanation of the User 2 User communication over the internet.
Thanks for the kind words =)
Thank You very much for this explanition
You’re welcome =)
Best article i have seen so far on L2/L3. Glad i found your article and i plan to read all your articles..
thanks very much.
You’re welcome =) Glad you liked it.
Simple and explanatory but also detailed with super animations.
You are talented. I will definitely read more.
Thank you..
You’re welcome!
Wish I had your brain dude. Outstanding. I just took a picture of this whole series in my head. Very well organized. Can’t forget it now
Awesome =) Hope it helps you in your studies and Networking journey!