This article is a part of a series on Address Resolution Protocol (ARP). Use the navigation boxes to view the rest of the articles.
We’ve discussed the use cases and role of traditional ARP in the prior article of this series. In this article we will discuss Proxy ARP and its role and significance.
Proxy ARP occurs when one node is responding to an ARP request on behalf of another node.
Proxy ARP is not a malicious event, it occurs to enable connectivity between two hosts that wouldn’t otherwise be possible.
Original Use Case
The original thought process for Proxy ARP was to accommodate hosts with misconfigured subnet masks.
As we’ve discussed before, when a host is speaking to another host on the same IP network, the target for the ARP request is the other host’s IP address. If a host is speaking to another host on a different IP network, the target for the ARP request will be the Default Gateway’s IP address.
The item which tells a host whether another IP address is on the same network or a different network is the subnet mask. This topology will illustrate how it works:
Host A is configured with the IP address 10.0.0.11 and a subnet mask of 255.255.255.0 (or /24 in CIDR). Host A will consider any IP address in the range of 10.0.0.0 – 10.0.0.255 on its local network.
Host B is configured with the IP address 10.0.0.22 and misconfigured with a subnet mask of 255.255.0.0 (or /16 in CIDR). Host B will consider any IP address in the range of 10.0.0.0 – 10.0.255.255 on its local network.
Presume both of these hosts are trying to speak to Host D, which exists on a different network and has the IP address 10.0.4.44.
When Host A tries to speak to 10.0.4.44, it would (correctly) consider Host D on a different network and would use traditional ARP to send the packet to the default gateway.
However, when Host B tries to speak to 10.0.4.44, it would (incorrectly) consider Host D on the same network and would instead try to ARP for Host D’s MAC address directly.
Host B’s ARP Request will be broadcast to the local network, but will never make it across the Router to Host D. Therefore, the ARP Request will go unanswered, and Host B will be unable to communicate with Host D.
Unless the Router itself responds to Host B’s ARP Request on behalf of Host D – which is the exact definition of a Proxy ARP.
Here is the process in action (Host A is not pictured):
The ARP Response sent by the Router looks exactly like a normal ARP response. Host B will use the response to create an ARP mapping that states the IP 10.0.4.44 maps to the MAC address 0053.ffff.9999. All subsequent packets sent to Host D will use this MAC address in the L2 header.
So despite the misconfigured Subnet Mask, Host B will be able to speak to Host D, due to the Router’s heroic use of Proxy ARP.
That being said, it does impose additional work load on the Router. We used the specific example of Host D’s single IP address, but due to Host B’s misconfigured subnet mask there are roughly 65,000 IP addresses that Host B now considers on its local network. When in reality only about 250 could possibly exist on its local network.
So while Proxy ARP enabled connectivity in this example, it unfortunately does not scale indefinitely and should not be relied upon. The long term solution is to correct the misconfigured Subnet mask on Host B.
Moreover, this specific use case for Proxy ARP is based solely around enabling routing despite there being a misconfiguration. With Proxy ARP, Host B may never even realize it has an incorrect Subnet Mask.
There is another school of thought that instead would prefer Host B’s misconfiguration to cause the communication to fail in order for Host B to be notified that something is wrong. Thereby creating an opportunity for Host B to fix the root problem.
Many routers these days do not send Proxy ARPs by default for this very reason. Although most include a way to enable it if desired.
That said, there is a very important and legitimate use case for Proxy ARP — one which does not stem from a misconfiguration. We’ll take a look at it after exploring the Packet Structure for Proxy ARP next.
Proxy ARP Packet Structure
The ARP Request looks identical to the traditional ARP Request we looked at in the last article. In fact, it is a traditional ARP request, as the initiator of the ARP Request does not know whether the response will come in via proxy.
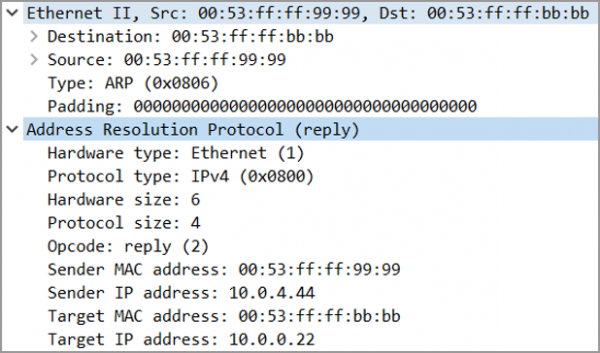
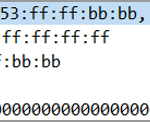
The Proxy ARP Response is slightly different, but has the same packet structure as the traditional ARP Response packet:
Notice the response is sent Unicast, directly from the Router’s MAC address to Host B’s MAC address.
The Opcode still contains the value 2, indicating an ARP response.
The crux of the Proxy ARP is in the Sender MAC and Sender IP address fields.
Notice, the Sender MAC address is the Router’s MAC address, but the Sender’s IP address is Host D’s IP address. The Router is providing its own MAC address as the owner for another hosts IP address, hence responding to the ARP on behalf of Host D.
Finally, the Target MAC and Target IP address fields, as expected, contain the information correlating to Host B, which is the intended recipient of this ARP Response.
Proxy ARP in Network Address Translation
Earlier we discussed Proxy ARP and its use case for routing for misconfigured hosts. Of course, that use case all but disappears if every host is configured properly.
However, there is a very legitimate and necessary use case for Proxy ARP, and that has to do with Network Address Translation, or NAT.
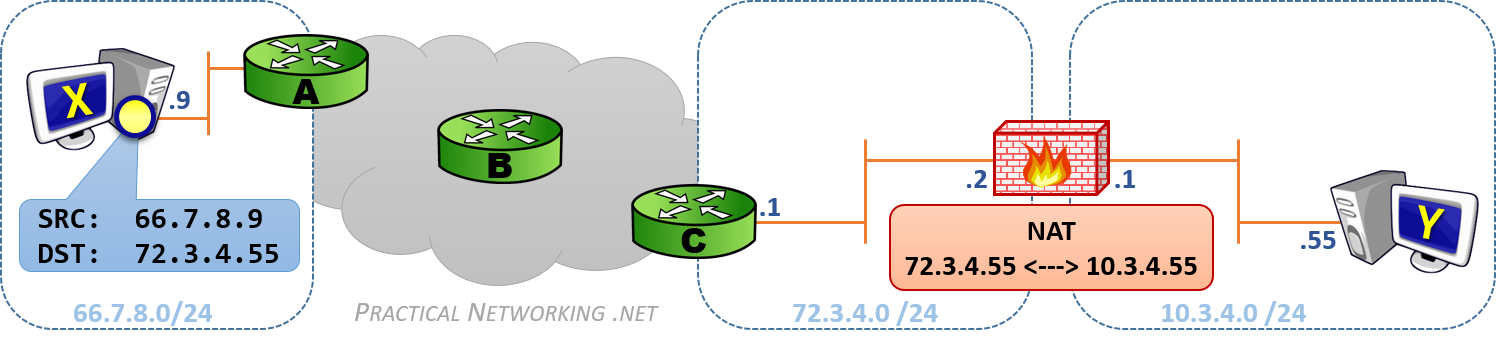
We will use this topology to describe it:
Our Firewall has the IP address 72.3.4.2 in the 72.3.4.0/24 network. Our Firewall is also configured with a Static NAT that translates the IP address 72.3.4.55 to 10.3.4.55. These IP addresses belong to Host Y, with the IP address 10.3.4.55. Host X is simply some host on the other side of the Internet, using the IP 66.7.8.9.
If Host X sends a packet to Host Y, that packet will have a Source IP of 66.7.8.9 and a Destination IP of 72.3.4.55. Routing will take that packet across the internet until it finally arrives at Router C.
Router C now needs to deliver a packet that is destined to a network it is directly attached to (72.3.4.0/24). Router C initiates an ARP Request to determine the MAC address which owns the IP address 72.3.4.55.
But the device which owns that IP address is Host Y, which is not in the same network as Router C. So Host Y would be unable to respond to this query.
The Firewall, however, having been configured to translate packets from 72.3.4.55 to 10.3.4.55, knows it must receive the packets destined to 72.3.4.55 so that it can translate them and deliver them to Host Y.
Therefore, the Firewall will use Proxy ARP to respond to Router C’s ARP Request for the 72.3.4.55 IP address on behalf of Host Y.
The entire process is illustrated in this animation:
If not for the Firewall participating in Proxy ARP, the Network Address Translation would fail, since packets sent from Router C would never arrive to the Firewall.
Hence, for Network Address Translation to work properly, the translation device must use Proxy ARP to properly receive packets to be translated.
As demonstrated, any NAT deployment will require the use of Proxy ARP to properly receive packets which must be translated.


Thank you so much for sharing this! Excellent explanation! =)
Well said,
The nat section is a great info
I have a question if you
Will the firwall then check the nat table and if entry found . It will replay with proxy arp ?
Hi Abdo, the Firewall would probably respond with a Proxy ARP whether a NAT table entry exists or not. Recall, some versions of NAT are bi-directional, and traffic must be able to arrive to the firewall whether it was initiated by the Internet host or the Inside host.
Hi,
Thanks for such detail articles. Finding them very useful. I have a question in this particular topic. Do you have a seperate firewall device or the firewall on the Host Y?
1. If Firewall on Host Y, then do we need the address translation, its as good Host Y owning the 72.x ip as well and any communication to 72.x IP will reach to it with direct routing and traditional arp.
2. If Firewall is external to it, does it have a different IP? And along with responding its own IP its also proxy responding to Host Y IP? (means the .1 and .2 interfaces on firewall have different IPs but are transparent to outside world?
Can you please elaborate. Thanks.
Hi Agveer,
#1 — If Host Y was on the same network as RouterC (72.3.4.x.0/24), then when RouterC issued the ARP request for 72.3.4.55
#2 — Yes, the Firewall has a different IP address (72.3.4.2) tan that of the translations.
Hi ed,
Actually with static NAT on a CISCO router, the proxy ARP is not needed. As soon as the static NAT command is entered, the router create a static ARP entry with his own mac-address.
For the (Inside Global) 72.3.4.55 10.3.4.55 (Inside local).
I guess the behavior is the same with real FW.
But thank you for the serie on ARP, i’ve learned some new things and other things are more clear now.
Hi PacketX,
Proxy ARP exists for the purpose of the upstream Router — not the Router or Firewall upon which the Static NAT is configured.
In the illustration, Router C needs an ARP mapping for the IP address
72.3.4.55. The Firewall is the device with the NAT configuration, and the Firewall must respond to the ARP Request sent by Router C. The Firewall is responding to the ARP Request by Proxy, i.e., on behalf of Host Y.i do not about Cisco ,but if it is sure, it is the same as this: create a sub/sec IP address,in this case 72.3.4.55/32(must different from the interface IP mask), then the interface will do the gratuitous ARP, so let the network know the arp info
Thank you for sharing this very good explantion! Very helpfull infos!
First, love the blog! Really helpful in starting my CCENT studying.
1. Just to clarify, if host Y were to respond to host X, would the source IP be 10.3.4.55? Would the firewall then change the L3 header with NAT translation?
Hi Josh, glad you like the blog!
To answer your question: Yes, you nailed it!
You can also learn more about Static NAT in this article from the Address Translation article series.
your explanation is very clear and useful
Thank you very much.
Thanks A LOT for helping beginners like me… Quick and Clear way of explanation is where You stand high…
Excellent explanation.. Thank you very much.
Proxy Arp will not take place for the Private IP of Y but for the Interface IP of the FW which will be configured on the external interface
Actually, it won’t take place for either. The Proxy ARP will occur for the Public IP of Host Y.
If the packet were sent to the Firewall’s Interface IP (.2), it would simply be a traditional ARP. But the packet is sent to Host Y’s Public address, and the Firewall must answer on behalf of Host Y.
Hey Ed,
Thanks for the wonderful articles.
They are really helpful i read types of Arp and its pretty sorted.
going through Vlan sections now
However i have few doubts.
when the packet at C asks for an Mac address for host 72.3.4.55 — what is host 72.3.4.55 here.
firewall? / some devices missing from the diagram?
Because provider edge router C is asking for the mac address of the customer edge device(firewall doing Natting)
then why do we need to enable proxy?
wont the layer 3 header be changed at customer edge device (firewall in your case)
confused ??? please assist ?
The “Provider Edge Router C” has a directly connected interface to the 72.3.4.0/24 network — anytime it tries to deliver a packet to anything in this range it will issue an ARP Request on that interface. See the finale of the Packet Traveling series for more details.
Remember, there might be many different hosts/firewalls/clients owning IP addresses in the 72.3.4.0/24 range. The firewall owns the IP address 72.3.4.2. The Firewall is also using the IP address 72.3.4.55 in a Static NAT for Host Y with the IP 10.3.4.55.
When the Router issues an ARP Request to resolve the IP 72.3.4.2, the Firewall will respond with an ARP Response.
When the Router issues an ARP Request to resolve the IP 72.3.4.55, the Firewall will respond on behalf of Host Y, due to the Static NAT configuration.
From the Router’s perspective, these ARP responses will look the same.
The L3 header between Router C and the Firewall will not be changed, the packet will be delivered to the Firewall with a destination IP address of 72.3.4.55. The Firewall will then change the L3 header to 10.3.4.55 to accommodate the Static NAT configuration.
ED,
In the routing table of C,
the next hop for the network 72.3.4.0/24 will be 72.23.4.2 or what?
generally wont it arp for 72.3.4.2 to reach 172.3.4.0 network// or since its a 1-1 mapping
it’ll arp 72.23.4.55 instead of 72.3.4.2 just because its static
is that what you mean?
The Routing Table of C will be a Directly Connected Route for 72.3.4.0/24 pointing out the “right” Interface.
Your articles are really helpful, because you do what most writers cannot achieve: You explain it in an understandable way.
But one thing in this part of the series is funny: Do you really want to state, that Proxy ARP is intended as a means to prevent missconfigured computers from not working??
😉
Yes, and as afnaan says, there are doubts. When you state that “the device which owns that IP address [72.3.4.55] is Host Y” this is not correct in my opinion. IP address of Host Y is 10.3.4.55. In your example 72.3.4.55 is the second IP address of the firewalls interface (beside 72.3.4.2). There is no need to do Proxy ARP (but to do NAT).
At this point you’re getting into semantics. Certainly, the case could be argued that the Firewall actually owns 72.3.4.55 (and not Host Y), and is therefore only responding to a ARP regularly (not via proxy).
It might be different for various Firewall manufacturers, but on the Cisco ASA, if you disable Proxy ARP, you disable the Firewall from responding to the ARP from Router C. And if Cisco is content calling that a Proxy ARP, I am inclined to agree ;).
Either way, NAT will still occur on the packet, that process is independent of the Proxy ARP. The Proxy ARP simply serves to get the packet to the Firewall, the Firewall can then do with the packet as it pleases.
>> But one thing in this part of the series is funny: Do you really want to state, that Proxy ARP is intended as a means to prevent missconfigured computers from not working??
Absolutely =)
Thanks Ed, that makes sense.
Hi I love your blog, it’s very informative:
Just a question.
Why Host Y has two IP addressess 72.3.4.55 and 10.3.4.55.
Is the IP address 72.3.4.55 belongs to Host Y or belong to Firewall.
Please Explain
Hi John,
Host Y has two IP addresses — a Publicly reachable address and a Private address. You can learn about the differences in this article about NAT.
As for whether Host Y or the Firewall owns the IP address 72.3.4.55, it can be argued either way.
Thanks Ed for this wonderful article on Proxy Arp.
Loved it…thanks much for sharing !! Cheers !!
thanks so much this is so helpfull and easy learned
Hi
Thanks for the detailed explaination.
I have a question say there is one more device Z with IP 10.3.4.56 and same public address 72.3.4.55 is configured as NAT for device Z. In this case when HOST X sends arp request with dest IP as 72.3.4.55 what will the returned mac address .. is it Host Y mac or Host Z mac???
Regards,
Rakshith.
Hi Rakshith.
Host X will not send an ARP for either of those IP addresses, it will send the packet to Router A (Host X’s default gateway).
When the packet gets to Router C, Router C will send an ARP for 72.3.4.55, and the Firewall will respond with the Firewall’s MAC address. The firewall is answering on behalf of Host Y and Z, based upon the Static Translations that are configured. The firewall is therefore performing a Proxy ARP.
Hope it helps.
Hi and thanks for the explanation.
One question though, I have a similiar situation in my network and I always disable proxy arp on interfaces, however NAT seems to bypass it. How come?
Hi Edo. Depending on the addresses you are using in NAT, it’s possible NAT will not function without Proxy ARP. When you disable Proxy ARP, it might just be disabling the first use case for Proxy ARP above. But that is just a guess, it’s probably different for each vendor and router. You’ll have to reach out to your device’s support channels.
Really lots of hard work done to make it simplest.
In fact i am beginner, but still I could understand.
Thanks Anil. Glad it all made sense =)
Internal/External Routing Protocols would also work in place of a static route.
Good Article
Thanks Mark. And yes, they would. Although in a way, they would simply automate the adding of a “static” route.
Hi, is this a Cisco-specific setup?
For my understanding, it makes no sense to do Proxy-ARP and DNAT at the same time?
In one case, there are two public addresses on the 72.3.4.0/24 facing interface of the firewall (72.3.4.2 and 72.3.4.55). In this case I can make a simple DNAT pointing to 10.3.4.55.
In the other case, the 72.3.4.55 is bound on Host-Y. In this case, Proxy-ARP on both Interfaces of the Firewall is required.
But why do you suggest Proxy-ARP and DNAT at the same time? Is this Cisco-specific?
Regards
No, this isn’t just a Cisco-ism.
> In one case, there are two public addresses on the 72.3.4.0/24 facing interface of the firewall (72.3.4.2 and 72.3.4.55). In this case I can make a simple DNAT pointing to 10.3.4.55.
Consider Router C. What will it do when it receives the packet with a destination IP address of 72.3.4.55. In particular, consider what address it ought to use as the L2 destination to get the frame to the Firewall.
You’ll find that unless you add specific configuration on Router C (i.e., a Static Route for 72.3.4.55 IP address), it will simply ARP to the entire 72.3.4.0/24 network. The Firewall in that case must respond with it’s own MAC address in order to receive the packet to begin with.
Is there a scenario where proxy arp would cause a firewall to respond for an external address where there is no NAT rule defined and create a potential IP conflict with other devices attached to router c?
To use your NAT illustration; traffic from 66.7.8.0/24, destined for a server host at 72.3.4.54/24 and connected to router c (it appears you have only a single address nat-ed and it is .55, not other addresses in 72.3.4.0/24 like .54, thus leaving them open for use by hosts like this fictitious server on .54).
Can you describe the conditions needed to cause this conflict situation, why this would be desirable behavior and how to work around it (perhaps intentionally create a nat for the 72.3.4.54/24 and set it to no-proxy-arp, thus removing this one address from arp response to router c and allowing the traffic to flow to the actual server host at 72.3.4.54/24?)?
Thank you for the help.
As BryanB’s colleague, to clarify, the scenario would be 2 firewalls attached to router C on the same 72.3.4.0/24 subnet with their own private networks behind them maintaining separate, non-conflicting IP’s and NAT tables. Would both firewalls respond to an ARP request if only one of them had a matching NAT table entry simply because they are on the same 72.3.4.0/24 subnet?
If so, how could that be avoided? The end goal is to have multiple tenants using the same public subnet without interference.
Hi Dustin / Bryan,
The question is borderline unanswerable without knowing the specifics of what firewall, what model, what configuration, and so on. So understand the answers below are broad strokes and will undoubtedly have exceptions.
That said… typically, no, a Firewall would not Proxy ARP for an IP address it does not have a NAT translation configured for. Moreover, if there weren’t any tricky Routing deployments, you would also not expect the FW to offer Proxy ARP for that reason as well.
However, you mentioned separate non-conflicting IPs and NAT tables — this leads me to believe there probably was a stray NAT configuration on one or the other Firewall which could easily have caused Proxy ARP for the other’s IP Space.
The scenario you describe:
> The end goal is to have multiple tenants using the same public subnet without interference.
Is a bit of an impossibility. If the tenants are controlling the Firewall, there is no shortage of harm they could cause (maliciously or inadvertently) to each other’s traffic. There are some Networking games you can play to limit this, but at the end of the day, if you want to remove the possibility of interference, they should not share the same IP network.
If you (the Admin) controls both Firewalls, then you ought to be able to set it up so one cannot affect the other, even if they are using shared IP space on the Outside.
Hope this helps. Feel free to reach out on Discord if you want to discuss it further. (pracnet.net/discord)
Hi Bryan, I responded to your colleague Dustin here.
Thank you Ed, particularly for giving BOTH answers; the technical one that explained that there would not normally be a proxy-arp response for an address that has no NAT defined behind it (this helps us with flexibility in how we use our addresses going forward), and then the ideal answer to limit risk in a multitenant situation (this will help us create a plan to limit risk in the future… from a tenant misconfigured NAT as just one example).
Much appreciated.
Thank you. This is a lot. It would have taken me through many books and websites to figure out incompletely. You make it easy as always.
Glad to help, Azza =).
I’m currently studying for Google and Amazon Security Engineering interviews. This tutorial series is straight gold, thank you.
Thank you for the kind words.
How did the Interviews go =) ?
Hi Ed, first I want to congratulate you for your amazing articles, I’m impressed with the didactics, and I put practicalnetworking in my TOP1. I’m not an expert in Computer Networks and I just started marathoning your articles to learn about this amazing world of Computer network. I have a question and if you can answer me. I think I’m confusing the process of the AND technique of a Local Address and a Remote Address, but I’ll ask anyway. Does Host B know that the Remote IP Address has a /24 CIDR? I say this because if Host B knew that Host D’s IP Address is a /24 it would know that 10.0.4.44 is not in its local network using the AND technique that compares the mask with the IP Address to find out what it is network and what is host. In this case “Host B” does not know the CIDR of the Remote IP Address and does it believe that the address 10.0.4.44 is a Class A /8 or Class B /16 address? Is that why “host B” will consider that the IP address “10.0.4.44” to be in the range 10.0.0.0– 10.0.255.255 and therefore it is on its local network? The “Host B” would know with from CIDR using AND technique that Local IP Address 10.0.0.22/16 cannot communicate with Remote IP Address 10.0.4.44/24 even though if the range of IP Address 10.0.0.22/16 goes from 10.0.0.0 untill 10.0.255.255
Hi John. Thanks for the kind words =). Glad you enjoy this content.
I think we answered your question on Discord. If you have any further, feel free to post there =). Cheers.
can we say local proxy arp works here because the ARP request is for another IP of the same subnet that is 72.3.4.55.
Proxy ARP is being used to instruct the upstream router (C, in my illustration) that packets sent to 72.3.4.55 should be sent to the MAC address of the Firewall.
thanks, bro, nice sharing, BTW, for some routers (such as Huawei) , I try to disable the prox arp(it is disabled by default), but it will still work for NAT, I use Wireshark to capture the package, I found the interface still do the Prox-arp resond.
Hello, nice article. There is another situation where proxy ARP is sometimes used. It is by wireless access points. Under normal conditions, ARP requests are broadcast to all clients. A WiFi access point sends the broadcasts to all associated WiFi clients. This can potentially eat up a lot of “airtime” and reduce performance of the WiFi network. To avoid this, some WAPs enable proxy ARP on the ethernet interface. Since the WAP will always know all of the MAC addresses of the WiFi clients connected to it, it can intercept incoming ARP requests from the ethernet side for clients associated to it, and respond with proper response for the WiFi client. Not all WAPs support this, and those that do may need it to be enabled manually in the configuration. Just FYI. Thanks.
i have read the Article ,but a bit confused as the address of host Y should be 10.3.4.55 as per diagram,but in the article it is mentioned ,that IP addrss of host Y is 72.3.4.55.
can any one clarify more.